Risk
Risk refers to threats an organization faces -- loss of earnings, loss of reputation, or harm of any kind. These articles explore the challenges of preventing, identifying and mitigating risk.
Risk can come in many forms, including financial issues, legal liabilities, strategic or leadership errors, or accidents and natural disasters. Today, IT- and data-related risks are growing concerns.
The following articles about risk look at the issue from many angles, especially from that of compliance officers and risk managers.
Preparing for Generation Z – The Future of the Front Line in Risk Management
Generation Z is poised to comprise nearly a quarter of the global workforce – and they’ll shortly become the first line of defense for most organizations. MetricStream COO Gaurav Kapoor discusses some unique attributes, expectations and risks associated with Gen Z. As Generation Z starts to enter the workforce, it will shortly make up almost a quarter of the global...
Enterprise Risk 2020: Are We Ready for Security 4.0?
G4S’ Rachelle Loyear points to several risk data points from ISACA’s recent State of Enterprise Risk Management survey, offers tactics to improve risk mitigation efforts and shares tips for learning from past industry trends. If you keep tabs on trends in cybersecurity, you’ll have noticed a lot of stories in the last year or two focusing on the Industry 4.0...
The True Cost of Website Inaccessibility
If you think retooling your website to be fully accessible is cost prohibitive, consider the cost of noncompliance. Deque Systems CEO Preety Kumar explores what a lack of accessibility can cost an organization. Legal action taken against companies for having websites, mobile apps and docs that aren’t accessible to those who are visually, hearing or cognitively impaired and more has...
What’s the Plan? – Planning a Post-Acquisition Merger Strategy
How should you plan your post-acquisition merger strategy? Jay Rosen continues his series on monitoring in an M&A context with this exploration of how to strategize the merger following an acquisition. To plan your post-acquisition merger strategy, first you should start with the Department of Justice (DOJ) and the information contained in various resolution documents on the DOJ’s website. These...
2019 Reputational Risk Study: Acknowledging Compliance Gaps
The court of public opinion often moves faster and perhaps more harshly than most courts of law. That's why The Red Flag Group surveyed business decision makers against 20 compelling questions to determine the importance of protecting reputation. The results? Interesting trends emerged here, as did the best practices that today's successful organizations are using to protect themselves from internal...
How to Drive Faster Action on Emerging Risks
Gartner’s Matt Shinkman discusses a sound strategy to increase executive urgency to address exposure to emerging risks, including building agreement on risk impact and presenting leadership with solution options. Gartner research suggests that 90 percent of risk leaders believe their companies need to act faster to get ahead of emerging risks. “Emerging risk” is defined as “a risk that does...
Intentional Control Design: Pillar 2 of the CRF for Cybersecurity and ERM
Cognitive governance is the first of five pillars making up the cognitive risk framework; the second is intentional control design. James Bone discusses chief considerations around intentional design. The five pillars of a cognitive risk framework are designed to provide a three-dimensional view of enterprise risks. In the last installment, cognitive governance (CogGov) was introduced as the first pillar. Its...
Engaging Social Media is More Effective Risk Management
Social media communication is a rarely implemented risk management tool, but it should get more play. Michael Toebe makes the case for why engaging, authentic use of social media is a real asset for corporate leaders and organizations. Increased development of social media communication can result in greater effectiveness of risk management, both internal to the organization and external. This...
What is the Board’s Role in Effective Risk Management?
The Shared Assessments Program, the member-driven leader in third-party risk assurance, recently released a new set of findings and recommendations developed with C-level executives and risk experts from a dozen organizations. The briefing paper provides boards of directors and C-level executives with new findings on the role of and increasingly crucial importance of board oversight, specific high-profile case study examples of...
Risk Managers: You’re Probably Spending Too Much Time Monitoring Email
Remember when email was the only way we shared information? Modern communication methods have evolved -- and risk has grown along with it. But you know that already, right? If you’re on this page, you might already have concerns relating to communication. With official conversations taking place on social media, on collaboration platforms like Slack and Microsoft Teams -- or...
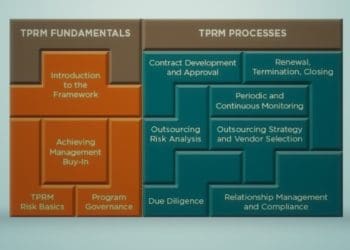
Shared Assessments’ Third-Party Risk Management Framework
The Shared Assessments member-led consortium for third-party risk management has introduced an assessment and monitoring module, the latest addition to the Third-Party Risk Management (TPRM) Framework trusted by cybersecurity, risk management, threat intelligence and compliance professionals worldwide. Instant Download: Read it Now Can’t see the download form? Disable your ad blocker.
NAVEX Global Strengthens Presence and Accelerates Growth in U.K. and Europe
Acquisition of Expolink and addition of new managing director are moves to support the region as new regulations proliferate LONDON (October 9, 2019) – In response to rapidly growing marketplace demand for its products, leading risk and compliance software and services company NAVEX Global® is expanding its presence in the U.K. and across the EU to serve a wider range of...