Browse by topic
New York State Bans Most Employers From Using Credit History in Employment Decisions
Amendment expands restriction NYC employers have been subject to since 2015
A Mid-Year Compliance Checklist for CA Wage Classification Risk
A federal proposed rule on contractor classification adds federal pressure to an already demanding California enforcement environment
(This Is a Lie) AI Is Inevitable
The only thing truly inevitable about AI is we can’t stop talking about it
Data Privacy Rules Built for Human Behavior Have an AI Agent Problem
Regulators are beginning to treat under-governed AI deployments as intentional conduct
AI’s Blend of Bias, Privacy & Regulatory Risk Means You Can’t Patch Your Way Out of Exposure
Take a system-wide view rather than attempting to plug holes
59% of Audit, GRC & IT Leaders Concerned About Shadow AI
More governance work, same governance team size; UK firms facing new AML requirements
FinCEN’s Proposed New AML Rules: What You Need to Know
The rule-making process is a culmination of years of moves toward standardizing financial institutions’ AML/CFT processes
On Antitrust Class Actions, You May Be Leaving Value in the Mailroom
The opt-out window closes whether or not anyone in your legal department even knew it opened
The SEC Is Killing Its Climate Rule, but ESG Risk Remains
The roller coaster journey of the SEC’s rules on public company reporting of climate-related risk has reached another valley, though experts tell CCI’s Jennifer L. Gaskin that the ride isn’t over yet.
Canaries in the Coal Mine: Law’s Crashout Over AI Is Coming for Everyone
Shadow AI & lack of proper guardrails are problematic combination
If Risk Management Is Truly Integrated, Why Aren’t We Hiring That Way Yet?
Many job postings functionally conflate audit & risk
Telling the Story of Compliance
Storytelling elevates compliance policies from words on a page to real, human experience
Outsmarting Your Inner Critic
Giving self-doubt a separate personality can take away its power
SEC Moves to Formally Rescind Climate Reporting Rule
Requirements never effectively applied in face of immediate court battle
Stadium Booms & Megaprojects: How Construction Scale Is Driving Legal Risk
Litigation involving the San Francisco 49ers’ stadium and other cases shine a light on the cost that come with massive construction projects
Executive Order Targets College Athletics Compliance & Federal Funding
Trump's April order links sports compliance to federal grant, procurement eligibility
Your Compliance Dashboard Can’t Tell You Everything About Employee Relations
The first signal that you have a compliance problem is retaliation allegation rates
AI: Reliable or Reliably Unsafe?
Recent lawsuits over AI applicant-screening tools highlight important differences
Enron, Blue Bell & FTX: Revisiting Corporate Governance Failures
When board oversight strays, so do companies, and if board oversight doesn’t exist, well, that can lead to an $8 billion fraud. Protiviti’s Jim DeLoach continues his series on governance failures with three more examples that provide lessons in sound business decision-making.
How Compliance Officers Can Be Better Coaches
Integrate compliance, foster dialogue and reward good actions
The Most Overlooked Risk in the EU AI Act: Misunderstanding Your Role
The act applies to companies, even those outside Europe, if they use AI outputs in their EU operations
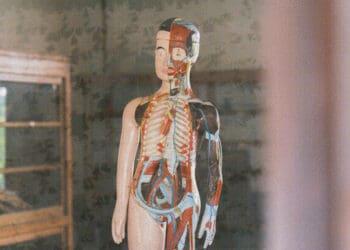
Why the Human Body Still Matters in an AI-Driven Workplace
Build short body-and-mood checks into risk meetings, and make it safe to say “something doesn’t feel right, but I can’t tell you why”
Global Operators Need to Take a Hard Look at Cuba Sanctions
Access to American banks and financial structures are at risk if companies cross the sanctions
Surveillance Pricing: You’re Watching Consumers — and Government Is Watching You
Practices that rely on consumer data or opaque pricing mechanics are increasingly evaluated through a consumer protection and data governance lens
Fewer Than Half of Execs Say Their Board Excels
Companies feel unprepared for fincrime; frontline workers aren’t thinking about compliance under pressure
SOC 2 Is Broken. The Delve Scandal Is Showing Us How.
Report published by the DeepDelver group shows just how thin the SOC 2 chain of trust can become under pressure
Compliant But Unprovable: Why Controls That Work Fail Examinations
Covering the gap between having compliance measures in place and the ability to prove they worked in a specific situation
The EU Is Making Forced Labor a Trade Compliance Problem, Not Just an ESG Issue
Most forced labor compliance frameworks ask companies to publish statements and describe their policies. The EU's new forced labor regulation operates differently — it gives authorities the power to block imports and pull products from shelves if forced labor is found anywhere in the supply chain. Arnall Golden Gregory attorneys Allison Raley and Nikita Kulkarni...
How You Handle AI Agents Says More Than You Might Think About Your Company’s Values
Are you really ready to deploy a virtual workforce?
Venezuela Energy Reform and US Sanctions Relief Are Moving Together. Here’s What That Means.
New OFAC general licenses create openings in Venezuela’s energy sector, but each carries different conditions