The technology industry today is transforming its approach to assessing and managing third parties for bribery and corruption risk. As if it wasn’t already a massive challenge for organizations to keep up with new and ever-changing legislation and regulations, FCPA enforcement has elevated to a whole new level of intensity with the DOJ putting heavy resources behind taking action.
But fines are just the tip of the iceberg, and even greater expense may be incurred in pre- and post-enforcement activity. Investigations and their associated legal fees often far exceed the actual fines. In many cases, they can run to five or 10 times more. Post-enforcement costs – updating policies, increased training and dealing with monitors – can also be significant and may last years. In addition, FCPA violations can have a damaging and public effect on a company’s reputation and long-term revenues.
The reality is that the many FCPA risks arise from relationships with third parties — agents, brokers, distributors, suppliers, etc. who may interact with foreign governments or agents. The following points are red flags that require input from your third parties:
- Points of contact with government officials and agencies
- Operations in known “high-risk” jurisdictions
Beyond the financial penalties, FCPA actions are likely to impact a company’s ability to raise capital, conduct merger activity and acquire contracts. When everyone in the company understands that it impacts the ability to make money and the company’s future, the FCPA conversation shifts from being a purely legal issue to its more proper designation as a general business issue that needs to be the on the radar screen of all business managers.
Given these factors combined, it is more important than ever for enterprise leaders to collaborate to reduce the cost, risk, inefficiencies and channel friction that currently exists. Major brands are coming to understand the importance of a new, collective approach and are teaming to solve the challenges and risks associated with third-party management together. One industry group, the Global Technology Distribution Council (GTDC), has decided to address the assumed resource issues and complexity of managing third-party risk head on by rationalizing effort and sharing the costs among its members.
Third-party management, anti-bribery/anti-corruption (ABAC) training, due diligence and vendor risk assessments are all measures that for the most part organizations recognize they should have in place – all key topics covered at a recent meeting of technology company executives hosted by Hiperos in Palo Alto, California. Yet the enormity and complexity of implementing anti-corruption compliance policies has companies struggling to properly and comprehensively manage the whole third-party landscape. In fact, research from Alix Partners highlights that while some companies have expanded how they engage with and audit their foreign subsidiaries, less than half (43 percent to be exact) regularly conduct due diligence on their third parties.
The catch is these programs often hit the back burner due to lack of funds, lack of awareness of risks until it is too late or inherent attitudes that “bad things cannot possibly happen to my enterprise.” The reality is, FCPA failures can happen at almost any company. Bad things can happen to a good company, especially when engaging third parties and not managing and monitoring them completely. Typical shortcomings include putting only policies and training in place, failing to perform a robust risk assessment before instituting the overall program, not considering all of the risks associated with countries or specific geographical regions and not integrating into the overall compliance program of the organization.
But today’s regulatory landscape dictates the need to act and, specifically, to be much smarter and more proactive about the management of third parties. The result of more enterprises collaborating and knowledge-sharing is a much-needed ripple effect. A larger sphere of knowledge, standards and best-practice sharing, in turn, creates awareness and actionable steps to understand and address the true risks posed by third-party partners and vendors.
In order to truly protect enterprises from bribery and corruption risks, organizations must put a simple, effective ABAC and third-party management program in place. It starts with risk identification. Understanding how the business could be at risk is vital. The first thing management should do is answer the following questions:
- Does the company do business in foreign markets?
- Do we or our third parties interact with government agents or officials and, if so, do we understand these points of contact?
Due diligence when it comes to accurately identifying risk and road-mapping a plan of coverage is the best method of protection because it helps companies understand the risks they are faced with and why these risks should be taken seriously. It’s important to keep in mind that FCPA is far from just a compliance problem. It is a business issue that needs to be managed progressively and holistically throughout the organization.
If you do business in any form with third parties outside the U.S., here are some action items and questions to consider:
- Make sure you know what partners and vendors do for the company.
- What are your due diligence procedures for engaging third parties?
- Assess which jurisdictions present the most operational risk.
- Conduct periodic compliance audits of third parties. Follow up on any red flags that may emerge during the relationship.
- Have your third parties agreed to your code of conduct?
- Review all points of contact with foreign officials.
- Check to see if any competitors or peers are under scrutiny. If so, you may be next.
- Review various departments such as sales, logistics, IT and marketing and identify high-risk functions.
- Determine if training procedures are robust and up-to-date.
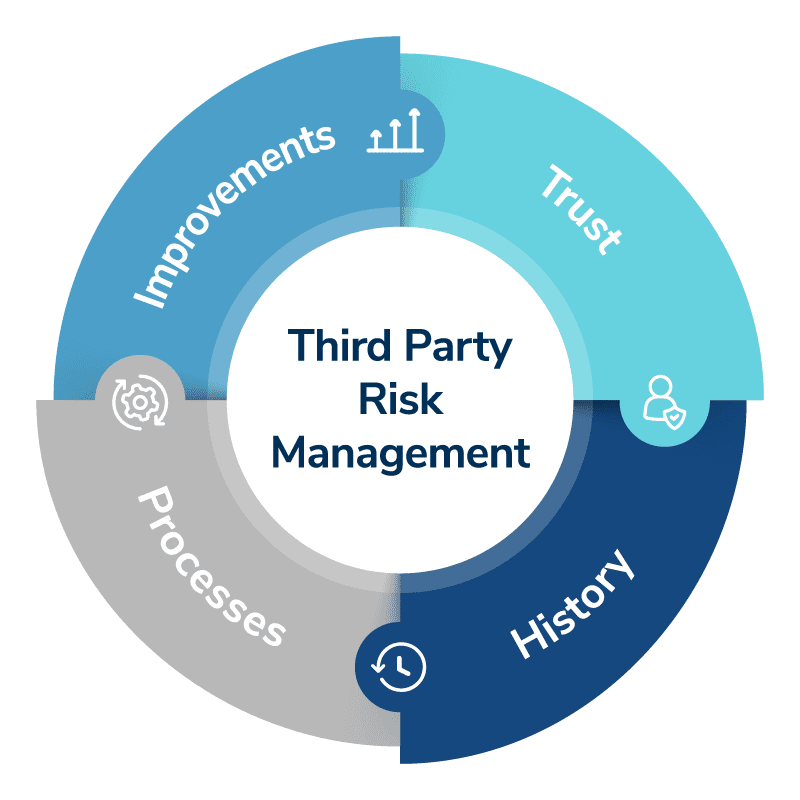
Here are the four ways to begin to make ABAC and third-party management implementation a reality:
- Know Your Third Parties: While it’s easy to outsource work to third parties, it’s not so easy to know who you’re actually doing business with and who is delivering the goods or services. Companies often default to only completing due diligence and managing a limited number of “high-risk” or high-spend third parties – or assuming that only traditional “IT vendors” pose an IT risk. Review whether your policies and technology allow you to identify, assess and manage all of your third parties for IT risk (as well as other risks of course).
- Know Their Business: It is not enough to hire third parties to help your company; you also have to know what business they are doing on your behalf. Ask yourself this question: If today you had to pull a list of which of your vendors or business partners have access to employee or customer personally identifiable information (PII) or to your IT systems, how long would it take? If you had to contact those companies for additional information, do you have accurate contact details?
- Know Their Risk: Less than half of companies regularly conduct due diligence on their third parties. While all third parties pose some level of risk, the risk and the level of seriousness differs dependent on the role of the third party. For example, third parties that deal with payroll or taxes usually pose a higher risk of security to your company’s data than the cleaning crew that comes in at night. Managing your third parties based on the risks that they pose requires knowing the risks in the first place and then having policies and procedures to control those risks throughout the life of the contract.
- Know Their Access: Not knowing that a third party had access to system passwords is not a valid excuse when your client’s records are stolen. Understanding what each party has access to – and why – will ensure that you have control over their access and can limit or deny access to sensitive information as appropriate.