Enforcing policies through proactive employee monitoring
Data breaches and fraud perpetrated by employees is an increasingly serious threat for businesses. Insider fraud rose 18 percent last year, according to Cifas’ Employee Fraudscape report, and reduced organizations’ bottom lines by as much as 5 percent, based on the latest study of ACFE (Association of Certified Fraud Examiners). Financial fraud expert Avivah Litan, an analyst for the Gartner research firm, recently stated that rogue insiders have emerged as one of the top two most malicious cyber crime threats to banking institutions.
One reason why insider fraud is so rampant is that it is typically difficult to detect. Employees who attempt to commit fraud are typically familiar with the controls that have been put in place and can try to circumvent them. For example, when companies require certain transactions to be authorized by a second employee, the fraudsters can work together to ensure that fraudulent activities are approved. Bank employees that know the size of the transactions that trigger a red flag for suspicious activity can siphon off smaller amounts of money over longer periods of time to avoid detection.
What motivates fraudsters
American Sociologist Dr. Donald Cressey analyzed the motivation behind fraud. According to his Fraud Triangle Theory, employees that commit fraud are influenced by rationalization, opportunity and motivation. They are typically not criminals, but may be facing financial or other personal problems such as gambling, drugs, alcohol addiction or excessive medical bills. Employees often rationalize their fraudulent behavior with thoughts like “I am just borrowing this. I will pay it back later.” Or they may take a moralistic approach like “I am using this money to help my family.”
Employees that commit fraud typically start small and then move on to bigger things. They may begin by accidentally stumbling upon an opportunity to view account details of a celebrity, executive or co-worker. While they may not necessarily use this information for personal gain, it may open their eyes to the possibility that they can breach security policies unnoticed. They may start to more systematically check the limits and controls that are put in place to see how they can bypass them. If they are successful and are not detected, their appetite will grow and they may continue by breaking bigger rules with larger financial and legal consequences for their employer.
The deterrence factor
Proactively monitoring employee behavior is the best form of prevention.
Take for example a case study of a credit card company with 3 million customers and over 1,500 employees that wanted to prevent their employees from snooping on the personal details of their celebrity customers. Internal controls were implemented for detecting employees who were viewing account information for public figures, and a system that proactively monitors employee behavior was put in place in order to track compliance.
After the first week, the security officer was shocked to receive 90 alerts that employees were viewing personal customer data they were not supposed to view, in most cases just out of curiosity. Once the security officer confronted these employees, the amount of alerts was significantly reduced, but still close to 20 employees continued to breach this security policy. It was only after an employee was dismissed for accessing sensitive data that was not required for performing his job that the alerts were no longer triggered. The company is confident now that employees are complying with the security policy. The level of incidents of suspicious activity is plotted in the graph below:
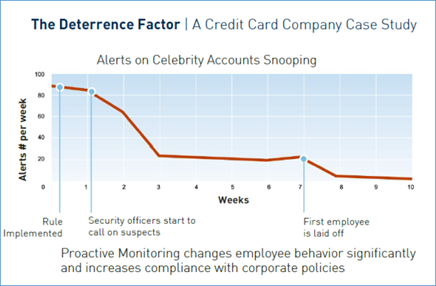
Implementing strict policies and educating employees is a good start, but in the end, monitoring and following up appropriately made the policies enforceable.
Given the opportunity, people who are motivated can rationalize their ability to commit fraud. But by monitoring behavior and by communicating to employees that their data access is being monitored, employees can avoid temptation and a company’s reputation and customer data can be secured.



 Hagai Schaffer leads Product Management and Marketing at Intellinx Ltd., a Bottomline Technologies company, and held the same position at Sabratec Ltd. He has over 25 years of experience in the software industry in both technology and business positions. Before joining Sabratec, Hagai served as CTO at Oblicore Inc., a leading provider of Service Level Management solutions. Prior to that, he held senior technology and business management positions with SPL WorldGroup. Hagai holds B.Sc., Mathematics & Computer Science (Cum Laude) and MBA (with distinction) from the Bar-Ilan University.
Hagai Schaffer leads Product Management and Marketing at Intellinx Ltd., a Bottomline Technologies company, and held the same position at Sabratec Ltd. He has over 25 years of experience in the software industry in both technology and business positions. Before joining Sabratec, Hagai served as CTO at Oblicore Inc., a leading provider of Service Level Management solutions. Prior to that, he held senior technology and business management positions with SPL WorldGroup. Hagai holds B.Sc., Mathematics & Computer Science (Cum Laude) and MBA (with distinction) from the Bar-Ilan University.









