The web of cybersecurity compliance organizations must navigate along with gaps between compliance framework design and effectiveness — among other stumbling blocks — can be serious barriers to effective risk management, says Steve Durbin, CEO of Information Security Forum. Overcoming these challenges begins by honestly auditing your current framework.
Talk to any CISO or cybersecurity leader about whether they are having compliance issues and they will resoundingly answer with a big “no.” The reality is that many organizations suffer from a compliance problem they may not be fully aware of.
Research from Creditsafe blamed general business pressures for driving companies to cut compliance corners. A striking 59% of 200 US professionals across accounting, legal, supply chain and consulting said they “always” compromise on compliance; 79% admitted to skipping compliance checks on customers and suppliers due to familiarity. Violations are on the rise — 67% reported more data privacy breaches, while 64% noted increased financial accounting and tax compliance violations.
Proper governance frameworks are without a doubt in place, and associated documentation exists. Policies and control standards might pass a cursory audit. The problem is that many organizations won’t be able to demonstrate in absolute terms whether their controls are working. You will be surprised how common this is. This happens because the compliance framework has structural issues.
Structural gaps occur because the technological environments in which organizations operate necessitate cross-jurisdictional regulations. They don’t have to comply with just one or two regulatory frameworks but with multiple frameworks, such as NIS2, DORA, HIPAA, SEC disclosure rules and others relevant to their industry and geography. Consequently, an organization’s capacity to manage compliance is failing to keep pace with the growing complexity of compliance demands.
Structural barriers impacting effective compliance
Compliance challenges rarely stem from a lack of intent. They are often rooted in how systems and processes are designed. To understand why gaps persist, it’s important to examine five structural barriers that limit effective compliance.
Fragmentation
A mix of compliance controls forms the frameworks of multinationals. An organization operating in the EU has to comply with GDPR, but the same organization with a footprint in the US must also comply with SOC 2. The organization might also have to comply with the NIST cybersecurity framework or industry-specific mandates like HIPAA and SOX. Controls across regions overlap, and the same control can get documented, evaluated and reported in multiple ways. This results in duplication of effort and inconsistent interpretation. The fix here is to swear by a harmonized control work, in which a unified reference point satisfies multiple regulatory regimes.
Language
Many organizations underestimate the power of language to create structural weaknesses in their compliance framework. Language, in this case, doesn’t mean English, French or Spanish. Language refers to how a security framework has been documented.
Traditionally, such documents were only for security professionals, but as the security footprint broadened and ownership extended into operations (finance, legal and business units), the security frameworks needed to be interpreted by key stakeholders. A framework that is only understood by a security engineer will ultimately face poor implementation. Governance documentation should be written in plain language that every stakeholder can understand.
How to Reassure Stakeholders When Facts Are Still Unknown During Cyber Incidents
Scenario planning and coordination between legal and communications experts allows organizations to build adaptable messaging
Read moreDetailsDesign and effectiveness gap
As the saying goes, there’s many a slip ’twixt the cup and the lip. The same is true for governance controls. Huge gaps can form between design and function. Regulators are becoming more explicit about the design’s workability.
For instance, NIS2 not only asks whether a set of controls is implemented, but it also demands proof that these controls are functioning as intended on an ongoing basis. This cannot happen without structured metrics mapped to specific control objectives. These objectives may be the percentage of critical vulnerabilities remediated or the number of unpatched critical vulnerabilities over time among others.
It’s simple: If a control cannot be measured, how can you depend on it for risk management?
Proportionality
A one-size-fits-all compliance framework will be counterproductive. A low-risk environment will see deployment of controls, processes or safeguards that are needlessly complex or stricter than the actual risk justifies. On the other hand, high-risk environments will see under-engineering, weakening their cybersecurity posture.
Modular design, starting with a baseline of core controls, followed by progressively rigorous requirements for high-risk environments, is the way forward. This also matters as new domains emerge. AI, operational technology and post-quantum cryptography are introducing control requirements that existing frameworks are still catching up with. A modular architecture makes it possible to add new domains without tearing down what already exists.
Culture
Verizon reports that about 60% of breaches feature a human element. A lack of genuine human buy-in can lead to gaps in cybersecurity posture, regardless of the sophistication, scope or scale of controls.
Lest we forget, security controls are owned and run by people, and it is these individuals who should best understand them and immediately flag concerns when they feel something is amiss. Culture and technical design working in tandem will help ensure a robust compliance framework.
The roadmap toward improved compliance
To improve compliance, begin by honestly auditing your current framework, identifying overlaps, inconsistencies and gaps. This will help identify fragmentation and set the stage for building a more harmonized compliance framework by preventing duplication and creating a master reference mapping to all relevant standards.
But this won’t deliver value without rewriting governance documentation for a business audience, especially those who own controls. The point is to remove inconsistencies.
Implementation without metrics lacks direction and impact. Define ideal performance, evidence and which thresholds signal the most problems. Lastly, think of all compliance output as risk intelligence that helps identify gaps in the framework, allowing for quick remediation.
With effective compliance, you are not just satisfying a regulator but managing your risks. Don’t treat compliance as a periodic obligation but as an effective mechanism for understanding, measuring and managing cyber risk. Compliance as a destination is not as important as the journey that helps you get there.



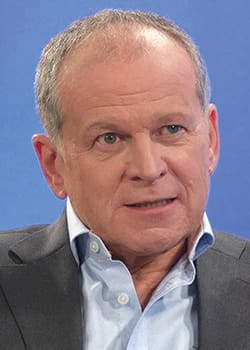 Steve Durbin is CEO of the Information Security Forum, an independent association dedicated to investigating, clarifying and resolving key issues in information security and risk management by developing best practice methodologies, processes and solutions that meet the business needs of its members.
Steve Durbin is CEO of the Information Security Forum, an independent association dedicated to investigating, clarifying and resolving key issues in information security and risk management by developing best practice methodologies, processes and solutions that meet the business needs of its members.