The Risk and Cost Benefit of Maturing 22 Key Processes
The Information Governance Process Maturity Model (IGPMM), developed by the Compliance, Governance and Oversight Council (CGOC) in 2012, has become a standard foundation for starting and revising enterprise information governance programs. The CGOC has now released a new version of the model to help organizations deal with today’s information realities.
Back in 2012, visionary members of the Compliance, Governance and Oversight Counsel (CGOC) recognized the need for a comprehensive process model to help organizations establish and maintain a more robust information governance (IG) program. They developed the first Information Governance Process Maturity Model, which has become a standard foundation for starting and revising enterprise IG programs. Since that time, however, the torrid growth of digital data, an increasingly complex and costly regulatory environment, cloud adoption and machine learning have put an ever-increasing strain on enterprise IG efforts, leading the CGOC to issue an update to the Maturity Model that reflects today’s more complex data challenges.
The total volume of information around the world is now doubling every two years and is expected to reach 180 zettabytes by 2025. According to one estimate, 2.5 exabytes of data are now produced every day, the equivalent of 530 million songs or 250,000 Libraries of Congress. Many large organizations are already storing a petabyte or more of data, which can cost them up to $2.8 million every three years. Thousands of other organizations are catching up quickly, and the problem will only get worse as business users struggle to find the information they need and make optimal use of it.
Of even greater concern to many organizations is the complexity of evolving regulations around the world and the increasing cost of data breaches and compliance failures. The EU, for example, has adopted the General Data Protection Regulation (GDPR), which has substantial fines for noncompliance and applies to any company around the world doing business in the EU. Even without the implementation of the GDPR in May of 2018, the 2016 Ponemon Institute Cost of Data Breach Study revealed the average cost for each lost or stolen record containing sensitive and confidential information has increased from $154 to $158. This means that even a breach of a relatively modest 30,000 records can cost more than $4.6 million. Many breaches, such as those at Yahoo, Home Depot and Premera Blue Cross, have run into the tens of millions of records and negatively impacted share price. In the case of Yahoo, the breach may even affect its terms of acquisition by Verizon.
Two other developments are reshaping IG practices, as well. First, organizations are increasingly relying on the cloud for applications and data storage, introducing IG challenges around classification, over-retention, shadow IT and geo-location. Second, an increasing amount of planning around the use of analytics and machine learning for major data initiatives is taking place without adequate consideration of the legal, ethical and compliance consequences.
Minimizing Enterprise Risks and Ensuring Ongoing Compliance
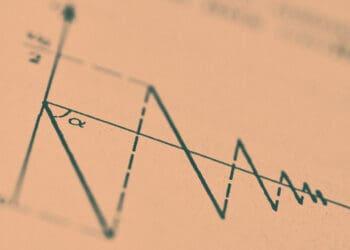
The basic proposition of the CGOC Information Governance Process Maturity Model is that as information ages, its value declines – while the cost to manage it stays relatively constant (increasing as the amount of data increases), and the cost of e-discovery and compliance risks actually rise. This widening gap between the business value information provides and the costs and risks associated with it should compel organizations to focus on improving their “information economics.”
Improving information economics depends on maturing 22 processes that help identify – and improve the management of – information value, cost and risk. The processes reflect the needs of the key information stakeholders, including legal, records information management (RIM), privacy and security, lines of business and IT. The maturation for each business process moves through four stages:
- Stage 1: Ad hoc and inconsistent
- Stage 2: Siloed and manual
- Stage 3: Siloed, consistent and instrumented
- Stage 4: Integrated, instrumented and optimized.
As they work through each process, stakeholders and the organization as a whole are better able to determine information value, align cost to the changing value over time, minimize legal and regulatory risk and lower overall costs.
For example, the Maturity Model includes a process for information disposal and decommissioning that deals with IT’s inability to properly dispose of data and decommission information systems that may be causing unnecessary risk and legal or business expense.
- In Stage 1, the most immature, IT “keeps everything” because there is simply no systematic way to determine regulatory obligations or business value.
- In Stage 2, IT can manually configure systems to retain, hold, collect or dispose of data. Legal requirements can also be manually configured in some systems.
- In Stage 3, IT is able to deduplicate files, dispose of log files and respond to business requests to decommission applications. IT and legal routinely work together to determine if any open legal matters affect the decommissioning.
- In Stage 4, data is automatically deleted at the end of its retention period when no legal hold has been specified, and backup data is routinely and systematically overwritten. IT consistently analyzes the data source catalog to identify systems with low business value to proactively determine savings opportunities. Data disposal is transparently done based on documented preservation and retention obligations.
For IG professionals already familiar with the Information Governance Process Maturity Model, the key updates are in the areas of:
- Privacy and Security. A “Privacy and Data Protection Obligations” section addresses evolving data privacy concerns, including the impact of the GDPR, and a new cost lever, “Data Security: Cost Reduction through Process Maturity,” helps organizations measure the extent to which process improvements can lower the per capita cost of a data breach. Finally, three processes have been added relating to data security best practices:
- “External Intrusion” focuses on creating a framework for deterring, thwarting and identifying external bad actors.
- “Accidental Data Leakage” allows for developing safeguards around classifying confidential information and preventing it from leaving via the network or employee devices.
- “Insider Theft of Data” helps prevent employees from stealing information assets.
- Cloud Computing. A new “Cloud Computing” process is designed to ensure IG safeguards are applied to nontraditional procurement and provisioning channels such as cloud services.
- Data Quality. This “Data Quality and Data Lineage” process can help organizations ensure that data is accurate and serves its intended business or compliance purpose.
To download the new Model, please sign in as a member or complete the easy membership sign-up.