Cybersecurity
Cybersecurity is the practice of protecting data, software programs, systems, and networks from digital attacks. The purpose of cybersecurity is to defend those digital assets throughout the lifecycle of a threat and/or attack. Our cybersecurity blog posts and news articles are written for compliance officers, auditors, and legal professionals. They include expert insights, opinions, training opportunities, events, whitepapers, podcasts, and webinars.
Almost half of all data breaches take place in the cloud. And it’s little wonder why with the massive migration of enterprise operations to cloud environments. This shift has also brought to light the pressing need for new audit and...
Read moreDetailsNew cybersecurity requirements are coming for financial advisers and others in the financial services sector. While enforcement isn’t here yet, as Sean Wilke of IQ-EQ explains, the tools to put effective compliance in place are already within reach. Financial firms...
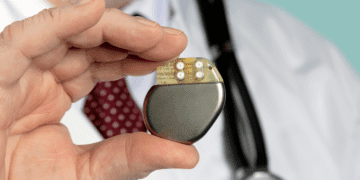
Read moreDetailsThe U.S., EU and China have issued stringent regulations that require automotive and medical device manufacturers to secure their products against cyber attacks. David Barzilai of Karamba Security explores how seemingly disparate industries overlap when it comes to consumer cybersecurity....
Read moreDetailsIncreasingly, companies are hiring chief data officers and chief data analytics officers to oversee their data environment. But while the need for these professionals is catching on, studies show they tend not to stay long. Manta CEO Tomas Kratky looks...
Read moreDetailsThe threat of cyber crime is nothing new for the average business. But new tools like AI mean fraudsters have access to even more sophisticated tools, enabling them to hyper-focus their attempts on high-value targets, including top executives and C-suite...
Read moreDetailsA hybrid communication environment has become the norm for most companies, from the use of messaging apps to communication systems. And while companies (and regulators) are cracking down on inappropriate use of these tools, as Theta Lake’s Stacey English explores,...
Read moreDetailsThe vast majority of Americans get their drinking water from public water systems, which are increasingly vulnerable to cyber attack thanks to reliance on automated, connected systems. ESG columnist John Peiserich explores a new EPA mandate designed to ensure these...
Read moreDetailsHow do today's top security leaders manage compliance? COMPLIANCE REPORT 2023 Securealities: Managing & Monetizing Multiple Frameworks What's in this report from Coalfire and Omdia: Today’s compliance assessment and assurance demands are continuously evolving and encompass every corner of the...
Read moreDetailsAbout six months from the splashy launch of Open AI’s ChatGPT and despite continued global regulatory concerns about AI’s proliferation, new research indicates that corporations are using the technology across their operations and are likely to keep expanding deployment of...
Read moreDetailsBy 2030, electric vehicles are expected to account for about 40% of all car sales in the U.S. While that’s good news for sustainability efforts, this transition will tax critical infrastructure, including increasing the risk of cyber attacks on EV...
Read moreDetailsSocial selling gives financial advisers an effective way to connect with potential clients and build a rapport with them as a way of generating new customers, but it also comes with compliance requirements that, if not managed properly, can become...
Read moreDetailsThe SEC is continuing its focus on cybersecurity regulations by announcing three new proposed rules and re-opening the comment period on an additional proposed rule from last year. Each of the proposed rules focuses on entities in the financial sector,...
Read moreDetails