A hybrid communication environment has become the norm for most companies, from the use of messaging apps to communication systems. And while companies (and regulators) are cracking down on inappropriate use of these tools, as Theta Lake’s Stacey English explores, finding the information they need remains a challenge for many companies.
Regardless of whether employees are working in an office, from home or a combination of both, they rely on modern communications tools to successfully do their jobs. These tools are efficient and effective but pose serious compliance and security risks to organizations when incorrectly used. Increasing amounts of personally identifiable information (PII) and personal health information (PHI) are being shared across platforms, and organizations are expected to be able to securely capture and retain, as well as retrieve and delete, this personal data.
If organizations do not use communications tools that support data protection and compliance capabilities and serve their employees’ needs, they risk severe compliance and security consequences.
In our recent survey of over 500 compliance and security professionals spanning various sectors, including global financial services, healthcare, insurance and government, we saw that a crackdown on data protection and non-compliant communications is afoot. Business leaders are prioritizing solutions to combat hacks, leaks and improper external communications.
Whaling: When Business Leaders Become Cyber Weapons
The threat of cyber crime is nothing new for the average business. But new tools like AI mean fraudsters have access to even more sophisticated tools, enabling them to hyper-focus their attempts on high-value targets, including top executives and C-suite members.
Read moreDetailsAmong the many threats against organization security and privacy, the survey found that files shared via chat are the greatest risk. This is largely because of the ease of sharing files of any size, which could contain confidential, sensitive or proprietary information. Following files shared via chat, the next two biggest threats to privacy and security are sharing links via chat or on-screen and risks associated with screen sharing.
While modern communications tools have benefited the workplace tremendously, they also provide plenty of opportunities for mistakes, breaches and data exposures to endanger an organization. As such, leadership must put safeguards in place to remain compliant and secure and possess the right tools to access data if needed.
Finding and extracting records and data is a critical component of compliance and security for any organization. In the event an organization finds itself in the crosshairs of an investigation or on the receiving end of a request for data, it needs to have the infrastructure in place to quickly locate and retrieve the required information. The compliance and security professionals interviewed in the survey reveal just how difficult a task this is for most organizations:
- 85% of all businesses in the survey report facing difficulties in retrieving information, with a majority stating the most difficult component being finding and extracting data.
- 52% of respondents find it easy to retrieve emails but difficult to search and retrieve content with chat, whiteboards, video and other modern communications.
- 33% need significant manual resources to search multiple systems and modes of communication.
- Only 15% are confident that they could retrieve all types of communication with ease.
Maintaining compliance and security should not be this difficult. To begin addressing these issues, organizations should evaluate legacy systems. There are a number of practical and incremental steps organizations can take to address any gaps in their current data protection coverage and capabilities:
- Ensure security and privacy policies reflect the new working reality and are understood by staff. That includes training and guidance on data security, record-keeping requirements and acceptable use of channels. Spot checks, internal audits, reviews and updates of existing policies should be part of the mix. Ensure that accountability and tone from the top reflect the importance of data protection and compliance.
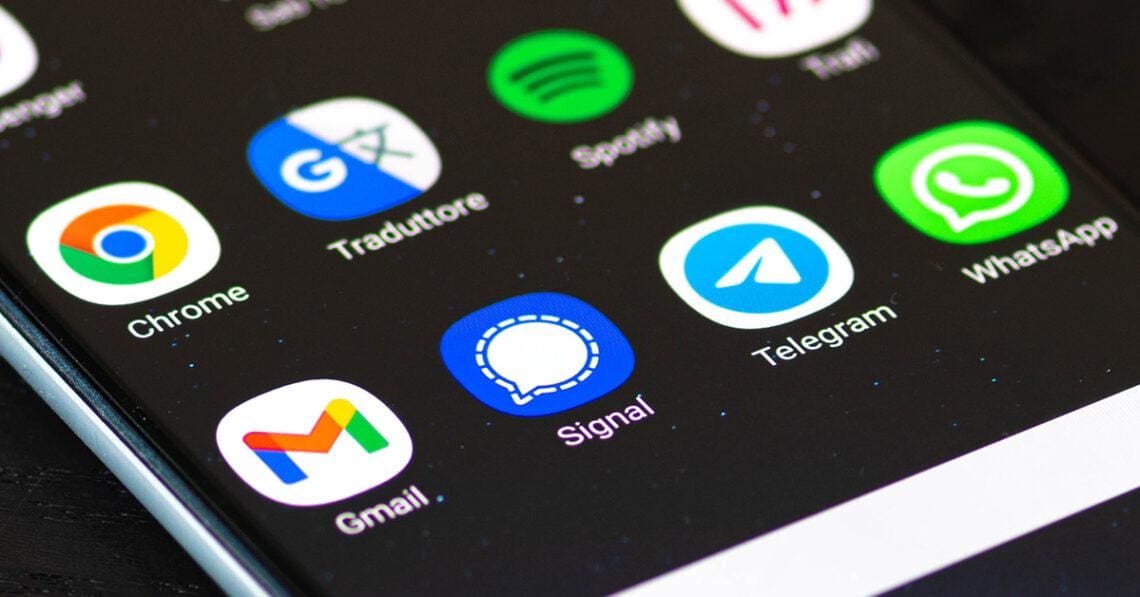
- Undertake a risk assessment of all communications channels to determine potential gaps in data protection, record keeping, oversight or information security. Check that all new communications modes like in-meeting chat, video, mobile, WhatsApp, file links, images and more are not only captured but also searchable and retrievable. Ensure effective security settings are in place on your meeting platforms.
- Take an incremental, risk-based approach. Start with addressing capture, archiving and supervision gaps in areas where data protection and other risks are highest, such as SMS, WhatsApp and other consumer messaging apps under regulatory scrutiny.
As work practices evolve, compliance and security practices must, too. With employees working remotely, in-office and a combination of both, organizations must take precautions to ensure the unified communications tools critical for their jobs are compliant and secure. The risks to confidential and proprietary data are too great to ignore.



 Stacey English is director of regulatory intelligence for Theta Lake, a collaboration compliance and security solutions provider. She has over 25 years' experience in financial services regulation and technology as a former regulator for the now-FCA and as a risk and compliance practitioner in global banks and insurers. For more than a decade, she led regulatory intelligence for Thomson Reuters providing regulatory insight to financial services firms, including global industry research covering conduct, culture and the cost of compliance. She’s also a Chartered Certified accountant with the highest result worldwide, a published author on conduct and accountability in financial services and an honorary fellow of Cambridge Judge Business School providing expert guidance to the Cambridge Centre for Alternative Finance.
Stacey English is director of regulatory intelligence for Theta Lake, a collaboration compliance and security solutions provider. She has over 25 years' experience in financial services regulation and technology as a former regulator for the now-FCA and as a risk and compliance practitioner in global banks and insurers. For more than a decade, she led regulatory intelligence for Thomson Reuters providing regulatory insight to financial services firms, including global industry research covering conduct, culture and the cost of compliance. She’s also a Chartered Certified accountant with the highest result worldwide, a published author on conduct and accountability in financial services and an honorary fellow of Cambridge Judge Business School providing expert guidance to the Cambridge Centre for Alternative Finance.